- Simply Cyber Newsletter
- Posts
- Simply Cyber Newsletter #180
Simply Cyber Newsletter #180
Crush Your Week Like a Cyber Pro with Simply Cyber!
Start your work week off at full speed with expert analysis and actionable intel from top cybersecurity news stories. Share with your End Users, Peers, and Executives to support weekly security awareness with the Simply Cyber Newsletter.
FOR END USERS
Social media scams cost Americans more than $2.1 billion last year, according to the FTC. Americans lost $2.1 billion to social media scams in 2025, with nearly 30% of reported scams starting on platforms like Facebook, Instagram, and WhatsApp. Investment, shopping, and romance scams drove the majority of losses, often using fake profiles, ads, and emotional manipulation.
What you need to know: Social media scams cost Americans $2.1 billion in 2025, an eightfold jump since 2020. Nearly 30% of reported scams now start on social platforms, and people lost more money to Facebook scams alone than to text and email scams combined. That should reshape how we train.
Help your users recognize the three patterns driving most losses:
• Investment scams use fake success stories and ""expert"" advice in ads or group chats.
• Shopping scams pull people to unfamiliar sites with deep discounts on familiar brands.
• Romance scams move slower, building trust before a sudden crisis that needs money.
The habit worth drilling is simple: pause before any money decision that touched social media. Never take financial advice from someone you only know online. Search a business name with ""scam"" or ""complaint"" before buying. Lock down privacy settings so attackers have less to work with.
AI is sharpening these scams fast, so keep your content current. Your users deserve training that matches what they're actually facing.
FOR PEERS
PyPI package with 1.1M monthly downloads hacked to push infostealer. A widely used PyPI package with 1.1 million monthly downloads was compromised to distribute an infostealer after attackers exploited a GitHub Actions flaw to forge a legitimate release. The malicious version stole developer credentials, cloud secrets, and crypto wallets, impacting unpinned environments.
What you need to know: Discuss with your peers how this incident shifts the supply chain conversation from account compromise to workflow exploitation. The attacker never touched maintainer credentials. They posted a malicious comment on a pull request that exploited a GitHub Actions script injection flaw, hijacked the workflow token, and used it to forge a signed release that flowed through the legitimate pipeline to PyPI and the Docker registry.
That detail matters because signed commits and official release channels were the trust signals that failed here. Peers should look at their own workflows for places where untrusted input like PR comments or branch names reaches a shell command. Anyone running unpinned versions of elementary-data 0.23.3 or the matching Docker tags should rotate every secret tied to CI, cloud, and registry access and rebuild from a known clean state.
FOR EXECUTIVES
ADT says customer data stolen in cyber intrusion. ADT confirmed a cyber intrusion exposing customer data including names, contact details, and partial Social Security and tax ID information. While no payment data or security systems were impacted, attackers claim up to 10 million records were stolen and are threatening a data leak.
What you need to know: Brief your executives on the ADT breach as part of a larger pattern, not a one-off incident. The attack is tied to ShinyHunters, the same group behind recent intrusions at Rockstar, McGraw Hill, Bumble, Match Group, and the University of Pennsylvania. The key question is whether your organization fits this targeting pattern and how prepared you are for the same playbook.
Two points deserve attention. First, watch the language your own comms team will reach for. ADT offered ""complimentary"" identity protection, but complimentary is a free upgrade at a hotel, not the bare minimum owed to people whose data you failed to protect. That word choice signals how a company sees its obligation, and customers notice. Second, ADT has disclosed multiple breaches over two years. Repeat incidents shift board and regulator focus toward systemic control failures, which is a conversation worth having before it is forced.
The World's Biggest Dev Event Hits Silicon Valley
From AI and cloud to DevOps and security — WeAreDevelopers World Congress brings the entire modern stack to San Jose. 500+ speakers. 10,000+ developers. One epic September. Use code GITPUSH26 for 10% off.

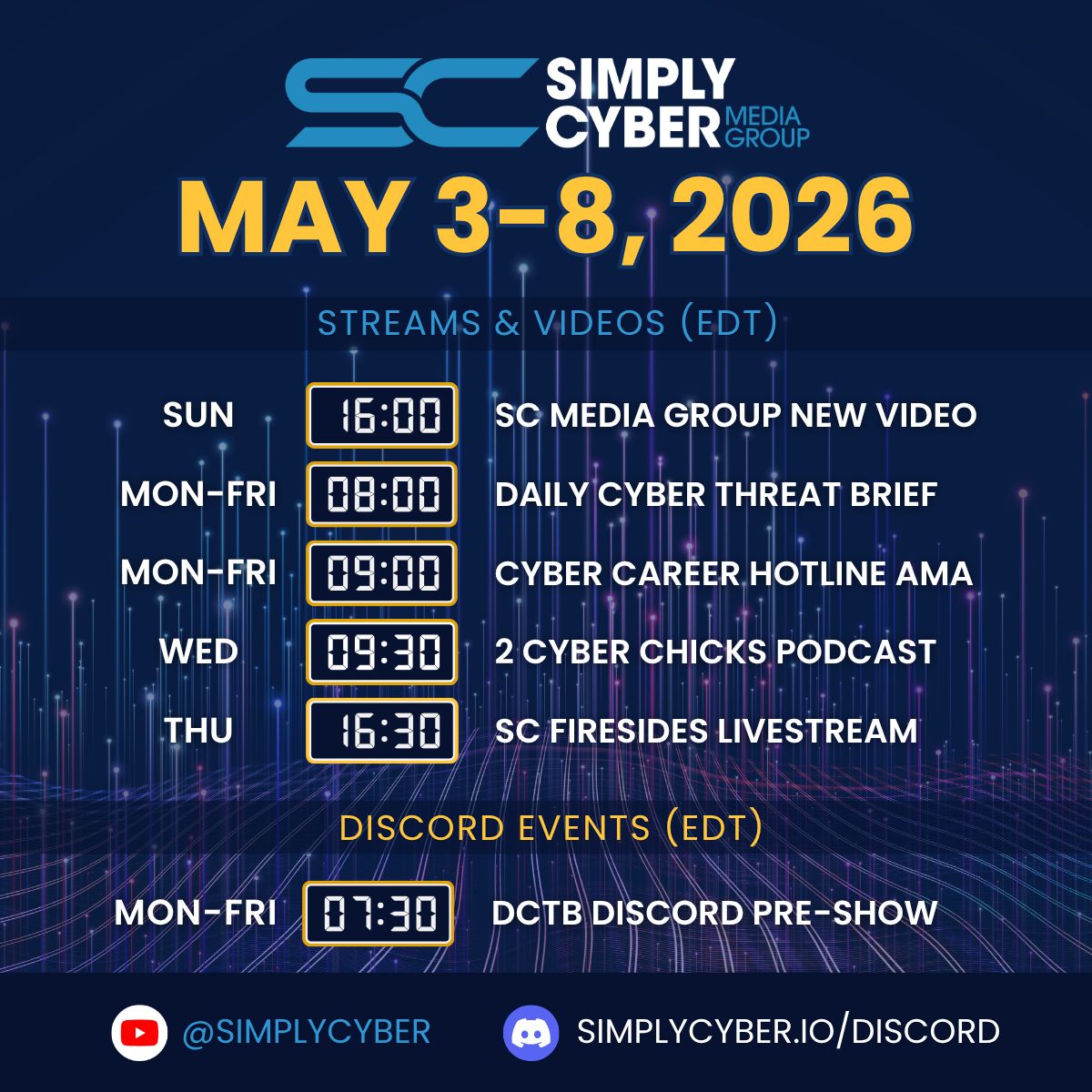
JOIN US EVERY WEEKDAY DAILY CYBER THREAT BRIEF
Gerald Auger, Ph.D. livestreams the Daily Cyber Threat Brief on Simply Cyber on weekdays at 8:00 AM EDT.
Join the party with cybersecurity enthusiasts and professionals alike who enjoy learning about the latest in cybersecurity news and staying connected.
Meet #TeamSC in live chat and join the community! https://simplycyber.io/streams
NEW VIDEO: SOC ANALYST INTERVIEW SERIES - PART 1
What does it actually take to pass a SOC analyst interview? We put three candidates - at different career levels - in the hot seat with one of the most common SOC interview questions you'll face.
Then Eric Capuano, a seasoned senior blue team veteran, breaks down exactly what separates the answers that get you hired from the ones that get you ghosted.
The Question:
You're a SOC analyst. You have 47 alerts and limited time. Four problems are on your screen right now:
- Multiple failed logins on a domain admin account
- Suspicious PowerShell activity on a developer machine
- 15 GB of outbound data transferred to an external cloud storage service
- 5 phishing emails reported by users
You can only work one. Which do you pick - and why?
Watch each candidate answer live, then hear Eric explain what he's actually listening for and what most candidates get wrong.
What You'll Learn:
- How experienced SOC analysts prioritize alerts under pressure
- Why "domain admin" is the two words that change everything in this question
- The common mistake candidates make by calling something "exfil" too early
- Why correlation should never be a manual, human-driven task
- How to stay calm and methodical when your queue is overflowing
Who This Is For:
- Aspiring SOC analysts, cybersecurity students, anyone preparing for a blue team or security operations role, and hiring managers who want to see what good looks like.
This is part of an ongoing series covering the most common SOC analyst interview questions with real candidate responses and expert commentary.
Watch now on Simply Cyber Media Group: https://youtu.be/t9LV5Hsew7c
SIMPLY CYBER SKILLS STREAM: Parsing Unsupported 3rd Party Apps with Jessica Hyde
Tuesday, May 5th at 1 PM EDT
In this presentation, Jessica Hyde teaches a methodology for mobile forensic analysis of unsupported applications and artifacts.
The methodology includes five parts to finding TRUTH in data.
- Track Down
- Recreate
- Unearth
- Translate
- Help others
These are necessary skills to parse 3rd party applications to tell factual stories and make scientifically logical inferences based on the presence or lack of data. We address common file locations, file system artifacts and their importance to mobile investigations, and how to make logical deductions based on recreating the digital environment with the same hardware and software.
By the end of your time with Jessica, you will have the skills necessary to go beyond the find evidence button to find truth in data that is commonly missed by forensic tools. This will enable the examiner to paint a more accurate depiction of the digital evidence.
Join us this Tuesday in live chat: https://youtube.com/live/e5NUdfV3Jyo
Register to attend and get notified: https://luma.com/nipa1nj2
SC MEDIA GROUP: 2 CYBER CHICKS - AI Hiring and Rejections
Wednesday, May 6th at 9:30 AM EDT
In this episode of 2 Cyber Chicks, Jax and guest co-host Tasha Denose sit down with Ruby Murphy, a technical recruiter known for her sharp boundaries, zero tolerance for nonsense, and deep expertise hiring across cybersecurity and engineering.
Ruby exposes what’s actually broken in tech and security hiring from AI-driven résumé black boxes to tone-deaf hiring practices that burn out candidates and recruiters alike.
The conversation explores:
- The recent New York Times lawsuit challenging AI “black box” hiring decisions
- Whether AI is making hiring fairer—or just more opaque
- Why candidates are getting rejected with no feedback and what recruiters see behind the scenes
- How to stand out professionally without playing performative LinkedIn games
- The hiring practices Ruby would happily burn down—and what should replace them
Ready for something blunt, human, and long overdue? If you’re a job seeker, hiring manager, or leader relying on AI to “scale” hiring - this conversation might make you uncomfortable - and that’s the point.
Join us this Wednesday on YouTube: https://youtu.be/dX9wItwISks
Register to attend and get notified: https://luma.com/72xkhvoz
SIMPLY CYBER FIRESIDES: HARDWARE HACKING
Thursday, May 5th at 4:30 PM EDT
Hardware is everywhere. From IoT devices to embedded systems, the attack surface is growing fast and many security teams are not prepared for it.
In this episode of Simply Cyber Firesides, host Gerald Auger, Ph.D. sits down with Matt Brown, Founder of Brown Fine Security, to explore what hardware hacking really looks like and why it matters for modern cybersecurity.
Matt specializes in IoT and OT penetration testing, with a focus on reverse engineering, vulnerability discovery, and embedded device security. His research has uncovered real-world risks in connected devices and has been featured in major publications. He also shares practical insights with a large online audience, helping others understand how hardware security works in practice.
🎯 In this episode of Simply Cyber Firesides, we explore:
• What hardware hacking means in real-world environments
• How attackers analyze and exploit embedded devices
• Common vulnerabilities in IoT and OT systems
• How reverse engineering plays a role in security testing
• Where AI and automation are starting to influence hardware security
• Why hardware security is becoming critical for defenders
This session is designed for cybersecurity professionals, penetration testers, and anyone interested in understanding how physical devices intersect with digital security.
Join us this Thursday Live on YouTube: https://youtube.com/live/86uu9TKMg1c
Register to attend and get notified: https://luma.com/d8o6ktf7
SC MEDIA GROUP WEEKLY EVENTS SCHEDULE
Join us for learning and networking every day of the work week at simplycyber.io/streams & meet the community at simplycyber.io/discord!
SIMPLY CYBER MONTHLY EVENTS LINEUP
Want to know what’s happening at Simply Cyber at any given time?
Head over to the SC Monthly Events Calendar to register for new and upcoming events for the month - don’t forget to subscribe! lu.ma/simplycyber
SC ACADEMY THE PLACE FOR CYBER CAREERS
At Simply Cyber Academy, we specialize in making GRC and Cybersecurity Careers a reality. Empower your career by learning real in-demand skills from cyber experts and the theory behind those skills with Simply Cyber Academy.
The popular GRC Analyst Master Class is a must for kickstarting your GRC Cybersecurity career. In addition, we have new courses covering various areas of focus in cyber available to help you advance in your career.
Check out the NEW FREE courses available in the academy!
SIMPLY CYBER ACADEMY BLOG HIGHLIGHT
Check out the highlighted blog on Simply Cyber Academy: https://academy.simplycyber.io/p/Blog?p=all-the-grc-analyst-answers-you-need
LET’S CONNECT
Stay current on trending topics, tips, events and resources in cybersecurity, connect with Simply Cyber on socials for new content.
As always, please send me feedback. Which tip above is your favorite? What do you want more or less of? Other suggestions? Please let me know. Just send a DM on X with #actionableintel in the subject so I can find it.
Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Find more about what’s happening this week in the Simply Cyber community, below. Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Thank you and see you again next week, #TeamSC!
Gerry