- Simply Cyber Newsletter
- Posts
- Simply Cyber Newsletter #177
Simply Cyber Newsletter #177
Crush Your Week Like a Cyber Pro with Simply Cyber!
Start your work week off at full speed with expert analysis and actionable intel from top cybersecurity news stories. Share with your End Users, Peers, and Executives to support weekly security awareness with the Simply Cyber Newsletter!
FOR END USERS
Hackers exploiting Acrobat Reader zero-day flaw since December. A zero day flaw in Adobe Acrobat Reader has been exploited since at least December. Attackers use malicious PDF files to steal data and gain full control of a victim’s system. No patch is available, and the attack requires nothing more than opening the file.
What you need to know: Most people treat PDFs as safe by default. This attack depends on that.
Researchers confirmed that opening a malicious PDF in Adobe Acrobat Reader is all it takes. No macros, no warnings to click through. Four months of active exploitation have passed with no patch available.
Until a fix is released, change how you handle PDFs and do not open files from senders you were not expecting, even if they look legitimate. If someone sent you a PDF you weren’t expecting, confirm it with them directly before opening it. For anything uncertain, use your browser’s built in PDF viewer instead of Adobe Reader, as it relies on different code and is not affected by this flaw.
FOR PEERS
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants. Attackers uploaded 36 malicious npm packages posing as Strapi plugins that execute code during installation. The packages harvest credentials, deploy reverse shells, and establish persistence using the privileges of the installing environment, including CI/CD pipelines and containers.
What you need to know: Researchers found 36 malicious npm packages mimicking Strapi CMS plugins, executing code at install time with no user interaction required. They harvested credentials, deployed reverse shells, and established persistent access using the full privileges of the installing user. These packages used plausible names and version numbers close enough to official plugins that a developer moving quickly would not question them. The payload executed during npm install through postinstall hooks, inheriting whatever access the environment allowed.
The useful internal question with your peers is not about these specific packages but around the trust architecture underneath your pipeline. Are postinstall scripts allowed to run without review? Do developers verify package scope? Official Strapi plugins live under @strapi/ - anything outside that is third party by default.
Do your CI/CD jobs actually need the privileges they run with, or is that inherited configuration no one has revisited? The question is not whether your developers are careful, but rather if your pipeline assume that they have to be.
FOR EXECUTIVES
US cybercrime losses pass $20B for first time as AI boosts online fraud. The FBI recorded $20.87 billion in cybercrime losses in 2025, surpassing $20 billion for the first time. Investment scams, business email compromise, and tech support fraud drove 85 percent of financial losses. AI-assisted schemes are increasing the scale and profitability of these attacks.
What you need to know: The headline number matters, but the composition matters more. Eighty five percent of reported losses came from fraud, not traditional intrusions. Investment scams, business email compromise, and tech support schemes are driving financial impact at scale.
AI is accelerating this trend by making impersonation easier and more convincing. The FBI attributed nearly $900 million in losses to AI-assisted scams, and the true number is likely higher. The result is not new types of attacks, but more believable versions of the ones that already work.
This makes visible a risk that was never fully inside the security team’s lane. Exposure now sits anywhere money can move or trust can be exploited, including finance, HR, and operations. This is a conversation worth having with your CFO and COO, not just your security team. What controls exist between a convincing request and an irreversible transaction?
The Gold Standard for AI News
AI keeps coming up at work, but you still don't get it?
That's exactly why 1M+ professionals working at Google, Meta, and OpenAI read Superhuman AI daily.
Here's what you get:
Daily AI news that matters for your career - Filtered from 1000s of sources so you know what affects your industry.
Step-by-step tutorials you can use immediately - Real prompts and workflows that solve actual business problems.
New AI tools tested and reviewed - We try everything to deliver tools that drive real results.
All in just 3 minutes a day

JOIN US EVERY WEEKDAY DAILY CYBER THREAT BRIEF
Gerald Auger, Ph.D. livestreams the Daily Cyber Threat Brief on Simply Cyber on weekdays at 8:00 AM EDT.
Join the party with cybersecurity enthusiasts and professionals alike who enjoy learning about the latest in cybersecurity news and staying connected.
Meet #TeamSC in live chat and join the community! https://simplycyber.io/streams
NEW VIDEO: THE SECURITY GAP NOBODY TALKS ABOUT
Ever wondered what separates a junior pentesting answer from a senior-level response? In this video, I asked three penetration testers at different career stages the SAME interview question - and the differences are eye-opening.
The Question: "You've successfully exploited a vulnerability and gained domain admin access during an internal pentest. Walk me through how you document this finding and what remediation guidance you'd provide."
Mike Saunders, Senior Red Team Professional at Red Siege, breaks down what hiring managers are actually listening for at each experience level. Whether you're trying to break into pentesting or leveling up to a senior role, this video will help you crush your next interview.
🎯 What You'll Learn:
✅ How to structure pentest findings in your reports
✅ The difference between technical findings and executive summaries
✅ Why confidence matters (and when to admit you don't know)
✅ How senior pentesters chain vulnerabilities and demonstrate business impact
✅ What separates good answers from great ones
Watch now on Simply Cyber Media Group: https://youtu.be/RzIsL3JhmYc
SIMPLY CYBER FIRESIDES: WHAT YOU NEED TO KNOW ABOUT AI WITH PHIL STAFFORD
Thursday, April 9th at 4:30 PM EDT
Artificial intelligence is rapidly becoming part of everyday cybersecurity operations, but many professionals are still trying to separate hype from reality. What should you actually understand about AI to stay relevant and make better decisions?
In this episode of Simply Cyber Firesides, host Gerald Auger, Ph.D. is joined by Phil Stafford, an AI Security Architect and researcher, to break down what matters most when it comes to AI in cybersecurity.
Phil works at the intersection of AI systems, security infrastructure, and business strategy. His experience includes building AI validation frameworks, working with multi-agent systems, and helping organizations think through how to adopt AI securely and effectively.
🎯 In this SC Firesides chat, we uncover:
• The fundamentals of AI that cybersecurity professionals should understand
• How AI is being used in real security environments today
• Risks and challenges introduced by AI systems
• How to evaluate AI tools and avoid common misconceptions
• What skills and knowledge will matter as AI continues to evolve
• How to think critically about AI outputs and decision making
This session is designed for cybersecurity practitioners, leaders, and anyone trying to make sense of how AI fits into their role and their organization.
Join us this Thursday in live chat - register to attend and get notifications: https://luma.com/dz8k7lpq
SC WOMEN IN CYBER MONTHLY MEETING
Meet the Simply Cyber Women in Cyber for the Monthly Meetup in Discord on Wednesday, April 15th at 1 PM EDT:
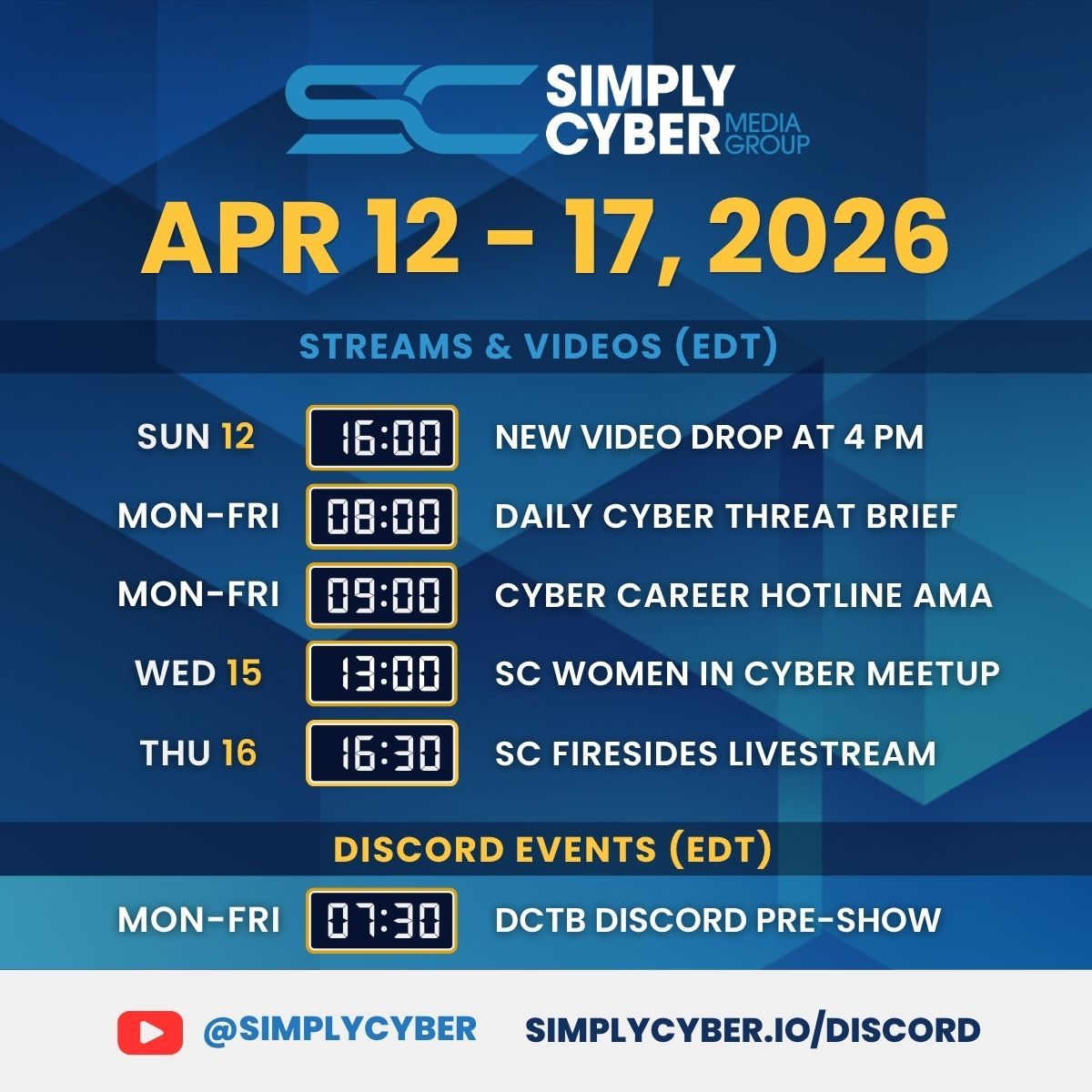
SC MEDIA GROUP WEEKLY EVENTS SCHEDULE
Join us for learning and networking every day of the work week at simplycyber.io/streams & meet the community at simplycyber.io/discord!
SIMPLY CYBER MONTHLY EVENTS LINEUP
Want to know what’s happening at Simply Cyber at any given time?
Head over to the SC Monthly Events Calendar to register for new and upcoming events for the month - don’t forget to subscribe! lu.ma/simplycyber
SC ACADEMY THE PLACE FOR CYBER CAREERS
At Simply Cyber Academy, we specialize in making GRC and Cybersecurity Careers a reality. Empower your career by learning real in-demand skills from cyber experts and the theory behind those skills with Simply Cyber Academy.
The popular GRC Analyst Master Class is a must for kickstarting your GRC Cybersecurity career. In addition, we have new courses covering various areas of focus in cyber available to help you advance in your career.
Check out the NEW FREE courses available in the academy!
SIMPLY CYBER ACADEMY BLOG HIGHLIGHT
Check out the blog from last week on Simply Cyber Academy: https://academy.simplycyber.io/p/Blog?p=soc-analysts-high-demand-why-it-matters
LET’S CONNECT
Stay current on trending topics, tips, events and resources in cybersecurity, connect with Simply Cyber on socials for new content.
As always, please send me feedback. Which tip above is your favorite? What do you want more or less of? Other suggestions? Please let me know. Just send a DM on X with #actionableintel in the subject so I can find it.
Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Find more about what’s happening this week in the Simply Cyber community, below. Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Thank you and see you again next week, #TeamSC!
Gerry