- Simply Cyber Newsletter
- Posts
- Simply Cyber Newsletter #173
Simply Cyber Newsletter #173
Crush Your Week Like a Cyber Pro with Simply Cyber!
Start your work week off at full speed with expert analysis and actionable intel from top cybersecurity news stories. Share with your End Users, Peers, and Executives to support weekly security awareness with the Simply Cyber Newsletter!
FOR END USERS
InstallFix' Attacks Spread Fake Claude Code Sites. Attackers are using Google-sponsored search results to distribute fake installation pages for Anthropic's Claude Code tool. Victims who copy and paste the malicious command install credential-stealing malware that can expose developer accounts and enterprise development environments.
What you need to know: Researchers at Push Security uncovered a campaign called "InstallFix" that spreads cloned Claude Code installation pages through Google ads. The pages look legitimate, but the commands users copy from them install Amatera Stealer malware instead of the real tool. The attack works because copying commands from websites into a terminal has become a common installation method for developers and AI tools.
Educate your end users that copying and running commands directly from websites carries the same risk as clicking unknown links. Encourage them to verify the official source before installing tools and to access installation instructions only from trusted vendor documentation. As more AI and developer tools rely on command-line installs, attackers are increasingly targeting this behavior. Teaching users to slow down and verify where commands originate can prevent malware from being executed with full system permissions.
As a bonus example, look at Friday’s story about attackers using SEO poisoning to distribute fake VPN software that steals credentials. It’s another real-world example you can use to educate end users about how search results and trusted platforms can be manipulated to deliver malware.
FOR PEERS
Medtech giant Stryker offline after Iran-linked wiper malware attack. Stryker reported a cyberattack that disrupted its Microsoft environment globally, affecting employee devices and access to internal systems while recovery efforts continue. The company stated it has not yet identified evidence of ransomware or traditional malware and is still investigating the root cause of the incident.
What you need to know: Share this story with your peers and consider the architectural risk it highlights. Organizations often focus on protecting endpoints from malware, but the systems used to manage those endpoints can become the real attack surface. If attackers gain access to enterprise management platforms or identity control planes, they may be able to issue legitimate administrative commands that turn off devices, revoke access, or disrupt operations at scale. The discussion worth having is whether those management systems are protected and monitored with the same rigor applied to domain administration or cloud control planes.
FOR EXECUTIVES
Google wraps up $32B acquisition of cloud cybersecurity startup Wiz. Google finalized its $32 billion acquisition of cloud security company Wiz, the largest acquisition in the company’s history. The move highlights how multi-cloud security visibility has become a strategic priority as organizations operate across multiple cloud platforms.
What you need to know: Google’s purchase of Wiz highlights a shift in how organizations must manage cloud risk. Many enterprises now operate across several cloud providers, making it difficult to maintain consistent visibility into assets, identities, and security exposures. Wiz built its platform around scanning cloud environments and presenting risks across infrastructure, applications, and runtime activity in a unified view. The takeaway is not the acquisition itself but the signal it sends about the direction of enterprise security. As organizations expand across multiple cloud environments and accelerate AI-assisted development, leadership should understand whether the organization has clear visibility into cloud assets and exposures, or whether risk is being assessed through disconnected tools and assumptions.
Go from AI overwhelmed to AI savvy professional
AI will eliminate 300 million jobs in the next 5 years.
Yours doesn't have to be one of them.
Here's how to future-proof your career:
Join the Superhuman AI newsletter - read by 1M+ professionals
Learn AI skills in 3 mins a day
Become the AI expert on your team

JOIN US EVERY WEEKDAY DAILY CYBER THREAT BRIEF
Gerald Auger, Ph.D. livestreams the Daily Cyber Threat Brief on Simply Cyber on weekdays at 8:00 AM EDT.
Join the party with cybersecurity enthusiasts and professionals alike who enjoy learning about the latest in cybersecurity news and staying connected.
Meet #TeamSC in live chat and join the community! https://simplycyber.io/streams
NEW VIDEO DROP: HOW JR., MID, & SR. PENTESTERS ANSWER THE SAME QUESTION
Pentesting interviews are not just about technical skill. They are about judgment, scope awareness, ethics, and how you think under pressure.
In this video, I ask three pentesters at different career levels the exact same real-world interview question: The scenario involves a phishing assessment, compromised credentials, and discovering sensitive employee behavior that raises serious legal and ethical concerns:
- An aspiring pentester trying to break into the field
- A mid-career pentester
- A senior pentester with over a decade of experience
To make this even more valuable, Mike Saunders, Senior Red Team professional at Red Siege, joins me to break down each answer and explain what hiring managers are actually listening for at every level.
Whether you are preparing for your first pentesting interview or aiming for a senior role, this breakdown will help you level up your answers and avoid common mistakes.
🎯 What You'll Learn:
✅ How interview expectations change from junior to senior pentester roles
✅ Why staying in scope matters more than flashy findings
✅ How hiring managers evaluate judgment, communication, and risk awareness
✅ How to handle sensitive discoveries during real engagements
✅ What turns a “good” answer into a standout answer
🔥 Special Thanks to Mike Saunders for his expert breakdown and hiring manager perspective.
🔔 Subscribe for more interview breakdowns covering pentesting, GRC, and SOC analyst questions. We're helping cybersecurity professionals level up their careers with practical, real-world insights.
Watch now: https://youtu.be/o5nhl0uLHrs
SIMPLY CYBER FIRESIDES: SABRINA CAPLIS
Thursday, March 19th at 4:30 PM EDT
Artificial intelligence governance is quickly emerging as one of the most important new domains in cybersecurity.
As organizations race to adopt AI technologies, they are also facing new questions about risk management, compliance, accountability, and security. This shift is creating an entirely new career path inside the cyber industry.
In this episode of Simply Cyber Firesides, host Gerald Auger, Ph.D. sits down with Sabrina Caplis, an AI Governance, Risk, and Security Consultant at RockCyber, to discuss how she built a career focused on helping organizations manage the risks associated with AI.
Sabrina works with large enterprises to develop AI governance frameworks, security controls, and risk management programs that align with emerging global regulations and standards. Her work focuses on helping organizations responsibly deploy AI while maintaining strong security and compliance practices.
Beyond consulting, Sabrina is active in the cybersecurity community. She serves on the boards of ISSA and ISACA Denver, contributes to the OWASP GenAI Security Project, and regularly shares insights on AI security and governance at industry events and forums.
Register now to attend and get notified with a calendar reminder: https://luma.com/lbpac3mp
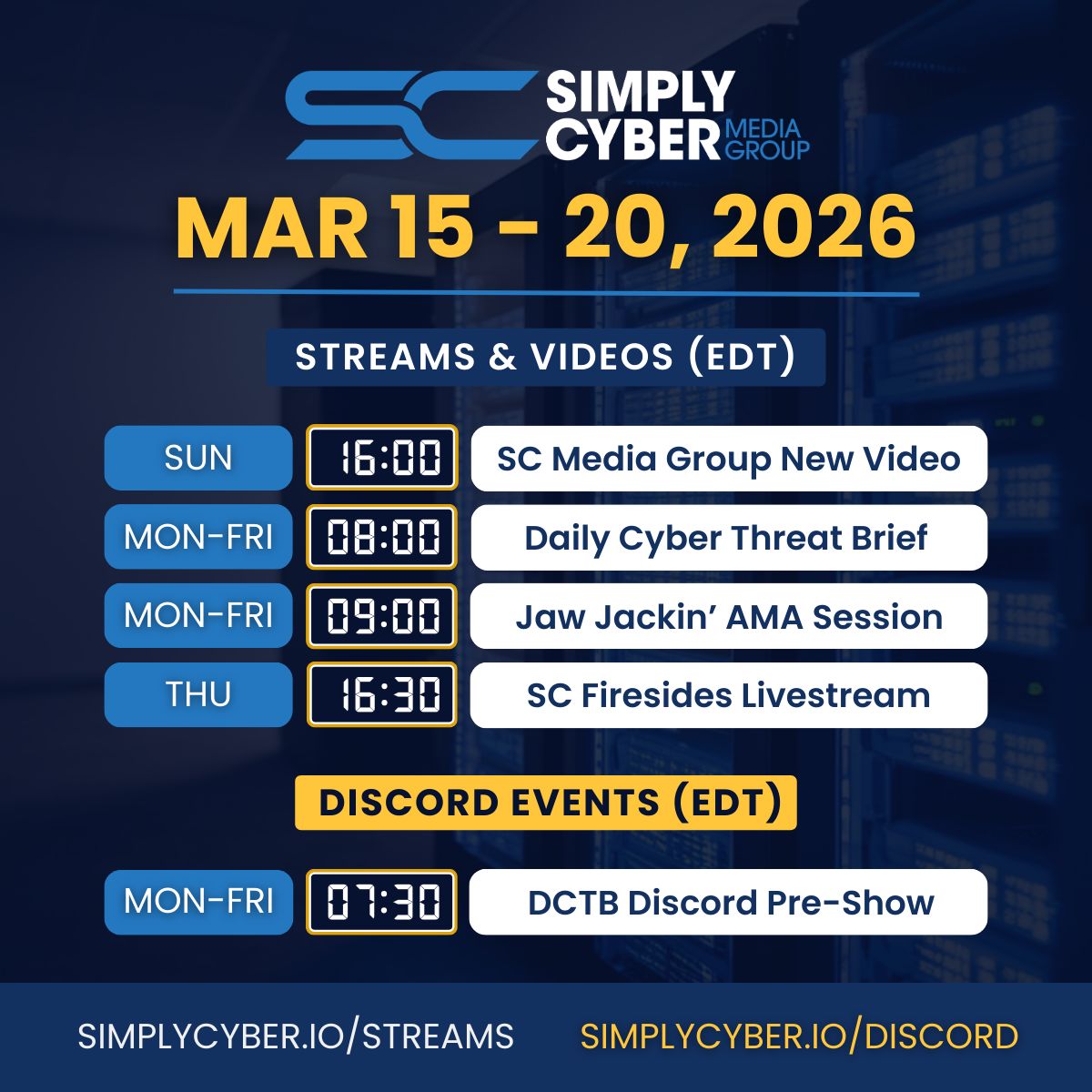
SC MEDIA GROUP WEEKLY EVENTS SCHEDULE
Join us for learning and networking every day of the work week at simplycyber.io/streams & meet the community at simplycyber.io/discord!
SIMPLY CYBER MONTHLY EVENTS LINEUP
Want to know what’s happening at Simply Cyber at any given time?
Head over to the SC Monthly Events Calendar to register for new and upcoming events for the month - don’t forget to subscribe! lu.ma/simplycyber
SC ACADEMY THE PLACE FOR CYBER CAREERS
At Simply Cyber Academy, we specialize in making GRC and Cybersecurity Careers a reality. Empower your career by learning real in-demand skills from cyber experts and the theory behind those skills with Simply Cyber Academy.
The popular GRC Analyst Master Class is a must for kickstarting your GRC Cybersecurity career. In addition, we have new courses covering various areas of focus in cyber available to help you advance in your career.
Check out the NEW FREE courses available in the academy and our new blog!
SC BLOG: ANALYZE YOUR LINKEDIN DATA WITH AI
Check out the blog from last week on Simply Cyber Academy: https://academy.simplycyber.io/p/Blog?p=analyze-your-linkedin-data-with-ai
LET’S CONNECT
Stay current on trending topics, tips, events and resources in cybersecurity, connect with Simply Cyber on socials for new content.
As always, please send me feedback. Which tip above is your favorite? What do you want more or less of? Other suggestions? Please let me know. Just send a DM on X with #actionableintel in the subject so I can find it.
Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Find more about what’s happening this week in the Simply Cyber community, below. Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Thank you and see you again next week, #TeamSC!
Gerry