- Simply Cyber Newsletter
- Posts
- Simply Cyber Newsletter #172
Simply Cyber Newsletter #172
Crush Your Week Like a Cyber Pro with Simply Cyber!
Start your work week off at full speed with expert analysis and actionable intel from top cybersecurity news stories. Share with your End Users, Peers, and Executives to support weekly security awareness with the Simply Cyber Newsletter!
FOR END USERS
Vulnerability Allowed Hijacking Chrome’s Gemini Live AI Assistant. A vulnerability in Chrome allowed malicious extensions to hijack the Gemini Live AI assistant and access sensitive resources like files, cameras, and microphones. While the flaw has been patched, the incident highlights how powerful browser tools can be abused if extensions are not carefully managed.
What you need to know: Chrome’s Gemini Live assistant can summarize webpages, perform tasks, and interact directly with what users see in the browser. Researchers discovered that a malicious extension could inject code into the AI panel and gain access to capabilities the extension would normally never have. In testing, this included reading local files, capturing screenshots, and accessing the camera or microphone. Google patched the issue in Chrome 143, but the underlying lesson remains: powerful browser tools create powerful opportunities for misuse if attackers can gain trusted access.
Speak with your end users about browser extensions and the growing power of AI assistants inside everyday tools. Many people treat extensions as harmless add-ons, but they often request deep access to browsing activity and web requests. Encourage users to install extensions only from trusted sources and to periodically review what they have installed. More importantly, teach them to notice unusual behavior. If a browser suddenly requests new permissions, activates the camera or microphone unexpectedly, or behaves differently after installing an extension, it should be treated as suspicious and reported. As AI assistants gain deeper access to systems, awareness of these signals becomes an important part of everyday digital safety.
FOR PEERS
Tycoon 2FA Phishing Platform Dismantled in Global Takedown. Authorities dismantled Tycoon 2FA, a phishing-as-a-service platform used to send tens of millions of emails monthly to over 500,000 organizations. The service enabled attackers to intercept login sessions and bypass multi-factor authentication to access email and cloud accounts.
What you need to know: Tycoon 2FA offered attackers ready-made phishing templates and infrastructure designed to capture authentication tokens during legitimate login flows. Microsoft estimates the platform was responsible for roughly 62% of the phishing attempts it blocked last year before authorities seized 330 domains tied to the operation.
Share this story with your peers and discuss how session-based phishing is changing assumptions around multi-factor authentication. MFA remains essential, but platforms like Tycoon 2FA show that attackers are increasingly targeting the authentication process itself rather than trying to break it. Many compromises now occur after credentials and session tokens are captured during normal authentication. The real discussion for security teams is whether phishing defenses, identity monitoring, and user education are keeping pace with these techniques, especially as phishing infrastructure becomes easier for less-skilled attackers to deploy at scale.
FOR EXECUTIVES
Google says 90 zero-days were exploited in attacks last year. Google tracked 90 zero-day vulnerabilities actively exploited in 2025, nearly half targeting enterprise infrastructure such as security appliances, networking platforms, VPNs, and virtualization systems. These are only the flaws researchers were able to confirm, meaning the true number of exploited vulnerabilities is likely higher.
What you need to know: The Google Threat Intelligence Group report highlights where attackers are concentrating their efforts. Nearly half of the exploited zero-days targeted enterprise infrastructure that controls network traffic and access between systems. Security appliances, VPNs, networking equipment, and virtualization platforms are particularly attractive because they provide privileged access across environments and often operate outside normal endpoint monitoring. The number itself matters less than what it represents: attackers are increasingly targeting the systems organizations depend on to secure and connect their networks. If this is raised with senior leadership, the decision to bring forward is whether these infrastructure systems are being treated as critical assets with defined monitoring and detection expectations, or whether they remain outside normal visibility simply because they are security tools.
Human-led. Rules-based. LLM-powered agentic systems. Each promises efficiency. Each has limits.
The real advantage? Knowing when, and how, to use them together.
The teams pulling ahead aren’t betting on a single model. They’re architecting a custom mix of all three.
On March 12th, join Tines and The Hacker News for Workflow clarity: Where AI fits in modern automation. You'll learn how to harness AI with clarity and control, and determine the right combination of workflows for you.
Register and learn more here.

JOIN US EVERY WEEKDAY DAILY CYBER THREAT BRIEF
Gerald Auger, Ph.D. livestreams the Daily Cyber Threat Brief on Simply Cyber on weekdays at 8:00 AM EST.
Join the party with cybersecurity enthusiasts and professionals alike who enjoy learning about the latest in cybersecurity news and staying connected.
Meet #TeamSC in live chat and join the community! https://simplycyber.io/streams
NEW VIDEO DROP: AI WON’T SAVE YOU
If you're a blue team analyst, SOC manager, or security operations professional evaluating AI tools, this video separates marketing hype from operational reality. Learn why AI makes good analysts great but won't fix bad analysts, how to actually deploy AI effectively, and why human-in-the-loop remains critical.
🔍 Key Takeaways:
✅ AI augments teams, it doesn't replace them
✅ Force multipliers only work if you have a force to multiply
✅ Fix your foundations before deploying AI tools
✅ Train your team first, then give them AI access
⚠️ Critical Points Covered:
- Why AI tools actually increase initial alert volume
- The hallucination problem vendors won't discuss
- Tool sprawl and license bloat challenges
- Garbage in, garbage out with AI models
- Pattern detection across millions of events
- Detection engineering acceleration
- Process documentation for AI effectiveness
Check out the video now from Simply Cyber Media Group: https://youtu.be/V8UN7owZFA0
SIMPLY CYBER SKILLS STREAM: AWS PRIVESC
Tuesday, March 10th at 1:00 PM EDT
Your AWS IAM policies might be one misconfiguration away from a full account takeover.
In this SC Skills Stream and hands-on webinar, Christophe Limpalair, a cloud security trainer with over 9 years of experience, will execute a live privilege escalation attack.
He'll then walk through the detection strategies, monitoring tools, and hardening techniques to stop it. You'll leave with a practical checklist you can apply to your AWS environment.
Topics covered:
- What a cloud PrivEsc is and how it works
- Demo of a live attack
- How to prevent and defend against this threat
Meet us in live chat and bring your questions for the Q&A session at the end!
Register now to attend and get notified with a calendar reminder: https://luma.com/5mq88nwx
2 CYBER CHICKS: How Women Are Rewriting the Rules of Cybersecurity Leadership
Wednesday, March 11th at 9:30 AM EDT
In this episode of 2 Cyber Chicks, we sit down with Aarti Gadhia, a cybersecurity leader who isn’t interested in fitting the mold, she’s here to redesign it.
We dig into what it really takes to lead in cybersecurity today: navigating perception versus reality, owning your voice in high-stakes environments, and pushing back against outdated leadership norms. Aarti shares her personal journey, the moments that shaped her confidence, and how she balances authenticity with executive presence in rooms that weren’t built with her in mind.
This is a candid, thoughtful, and energizing conversation about:
- What real leadership looks like in cyber (beyond titles)
- How women and underrepresented leaders shape influence without permission
- The unspoken rules of executive spaces—and when to break them
- Building credibility without losing yourself
If you’ve ever felt like you had to “perform” to be taken seriously in tech or security, this episode is for you.
Register today and get a calendar invite with link to remind you the day of the event! https://luma.com/hkwkxvrl
SIMPLY CYBER FIRESIDES: WITH KARLA REFFOLD
Thursday, March 12th at 4:30 PM EDT
Most organizations rely on scoring systems like CVSS or EPSS to determine cyber risk. But what if there's a better way?
In this episode of Simply Cyber Firesides, host Gerald Auger, Ph.D. is joined by Karla Reffold, Chief Insights Officer at Surefire Cyber, for a conversation about a different way to think about risk.
Karla leads with intelligence, research, and real incident data to help executives and responders make confident decisions under pressure. With a strong background in cyber threat intelligence and incident response strategy, she focuses on translating complex telemetry and threat data into insights that drive meaningful action.
🎯 In this SC Firesides episode, you will learn:
• How intelligence-led risk assessment works in practice
• The role of real-world incident data in evaluating exposure
• How to translate cyber risk into language executives understand
• A practical framework for calculating risk beyond static scoring models
This conversation challenges common assumptions and explores how security leaders can move from theoretical risk scoring to contextual, intelligence-driven decision making.
If you are responsible for vulnerability management, incident response, cyber intelligence, or executive reporting, this session will give you a fresh perspective on how risk should actually be measured.
Join us this Thursday in live chat: https://luma.com/4lcz4s5w
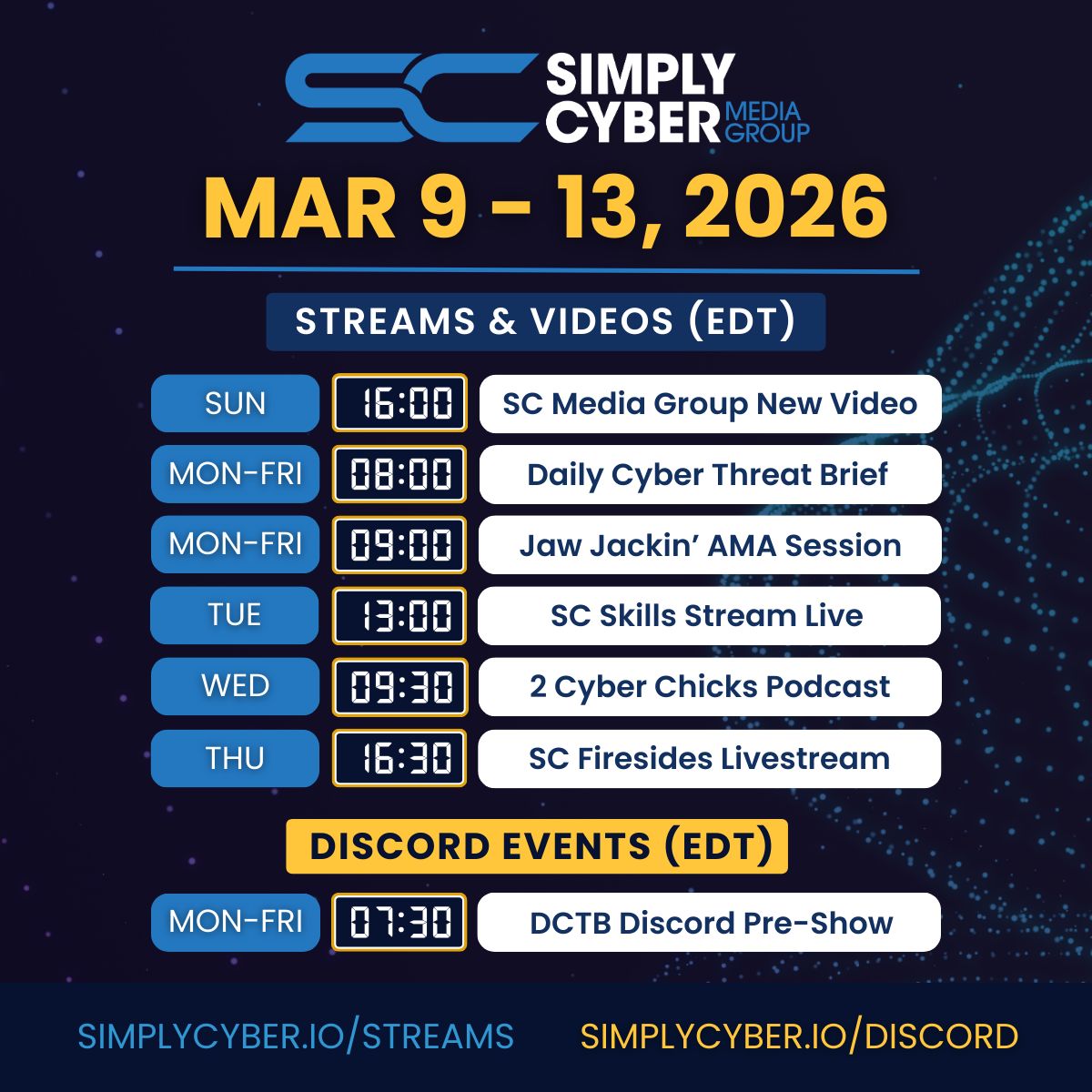
SC MEDIA GROUP WEEKLY EVENTS SCHEDULE
Join us for learning and networking every day of the work week at simplycyber.io/streams & meet the community at simplycyber.io/discord!
SIMPLY CYBER MONTHLY EVENTS LINEUP
Want to know what’s happening at Simply Cyber at any given time?
Head over to the SC Monthly Events Calendar to register for new and upcoming events for the month - don’t forget to subscribe! lu.ma/simplycyber
SC ACADEMY THE PLACE FOR CYBER CAREERS
At Simply Cyber Academy, we specialize in making GRC and Cybersecurity Careers a reality. Empower your career by learning real in-demand skills from cyber experts and the theory behind those skills with Simply Cyber Academy.
The popular GRC Analyst Master Class is a must for kickstarting your GRC Cybersecurity career. In addition, we have new courses covering various areas of focus in cyber available to help you advance in your career. Check out the NEW FREE courses available in the academy and our new blog!
LET’S CONNECT
Stay current on trending topics, tips, events and resources in cybersecurity, connect with Simply Cyber on socials for new content.
As always, please send me feedback. Which tip above is your favorite? What do you want more or less of? Other suggestions? Please let me know. Just send a DM on X with #actionableintel in the subject so I can find it.
Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Find more about what’s happening this week in the Simply Cyber community, below. Join us on the Daily Cyber Threat Brief happening every weekday morning at 8 AM Eastern on YouTube and LinkedIn.
Thank you and see you again next week, #TeamSC!
Gerry